If you run a rsyslog server using the rsyslog imtcp module with OpenSSL or GnuTLS enabled for encrypted communication support, chances are, as your infrastructure and/or log traffic grow, you will find out, that for TLS offloading, rsyslog is only able to use one thread of your multithreaded system. This is by design and until today, the imtcp module, which is also the only module supporting TLS, is not able to utilize multiple CPUs.
The imptcp, also known as plaintext-tcp module however, does support multiple threads, but cannot do any encryption.
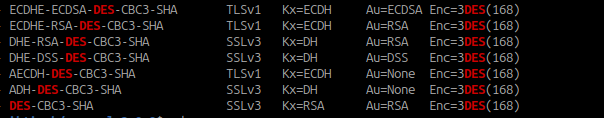
In my case, I found that the only viable solution to multithreaded TLS offloading with rsyslog is to wrap stunnel in front of it, like this in /etc/stunnel/rsyslog-server.conf:
(more…)